How Atlan connects to Oracle
Atlan connects to your Oracle database to extract technical metadata while maintaining network security and compliance. You can choose between Direct connectivity for databases available from the internet or Self-deployed runtime for databases that must remain behind your firewall.
Connect via direct network connection
Atlan's Oracle workflow establishes a direct network connection to your database from the Atlan SaaS tenant. This approach works when your Oracle database can accept connections from the internet.
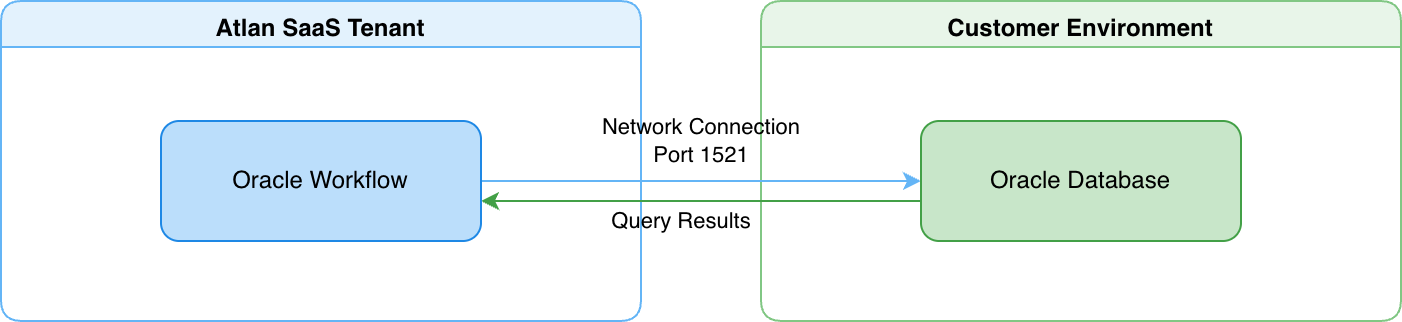
- Atlan's Oracle workflow connects directly to your database from the Atlan SaaS tenant over port 1521 (default).
- You provide connection details (hostname, port, SID, credentials) when creating a crawler workflow.
- Your Oracle database accepts inbound network connections from Atlan's IP addresses, controlled through your firewall rules or network security groups.
For details on how direct connectivity works, see Direct connectivity.
Connect via self-deployed runtime
A runtime service deployed within your network acts as a secure bridge between Atlan Cloud and your Oracle database. This approach works when your Oracle database must remain fully isolated behind your firewall.
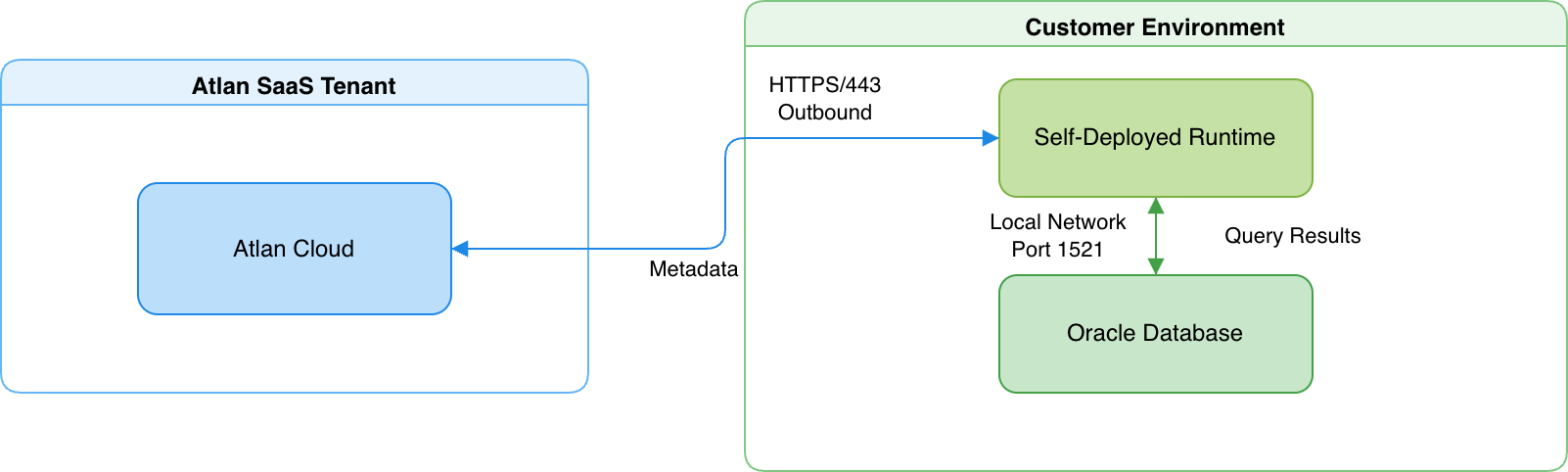
- The runtime maintains an outbound HTTPS connection to Atlan Cloud (port 443) and a local network connection to your Oracle database (port 1521).
- The runtime translates requests into SQL queries, executes them on your Oracle database, and returns the results to Atlan Cloud.
For details on how Self-Deployed Runtime works, see SDR connectivity.
Connection details
Atlan's Oracle connector uses a native Python driver stack to connect to your database—it doesn't use JDBC or require a Java runtime.
Driver and protocol
The connector communicates with Oracle using the python-oracledb driver through SQLAlchemy. It runs in thick mode with Oracle Instant Client, using the Oracle Net protocol (TCP or TCPS for encrypted connections). This is the same wire protocol used by Oracle's own tools—no translation layers or middleware are involved.
Connection pooling and sessions
During a metadata extraction workflow, the connector maintains a small pool of database connections:
- Connection pool: Up to 15 connections maximum (5 persistent + 10 overflow)
- Concurrent sessions: Up to 5 metadata extraction tasks run in parallel, each using its own database connection
- Query pattern: Each task executes read-only SELECT queries sequentially; multiple tasks may query the database at the same time
The connector acquires connections on demand and returns them to the pool after each query, keeping the connection footprint minimal.
Container and pluggable database connections
The connector connects to whichever database you specify in the connection credentials:
- If you provide a PDB service name, the connector connects directly to that PDB and extracts only that PDB's metadata. This is the most common configuration.
- If you provide a CDB service name or SID, the connector connects to the CDB root.
- The connector tries
SERVICE_NAMEfirst, then falls back toSIDif the service name isn't found.
Security
Atlan extracts only structural metadata—schemas, tables, and columns. For example, if you have a CUSTOMERS table with customer records, Atlan discovers the table structure and column definitions, but never queries or stores the customer records themselves.
-
Read-only operations: All database queries are read-only SELECT statements. The connector can't modify data, create or drop database objects, or change any configuration. The Oracle user permissions you grant control exactly what the connector can access.
-
Credential encryption: Oracle connection credentials are encrypted at rest and in transit. In Direct connectivity, Atlan encrypts credentials before storage. In Self-deployed runtime, credentials never leave your network perimeter—the runtime retrieves them from your enterprise-managed secret vaults (AWS Secrets Manager, Azure Key Vault, GCP Secret Manager, or HashiCorp Vault) only when needed, and Atlan Cloud never receives or stores them.
-
Network isolation with Self-deployed runtime: Your Oracle database gains complete network isolation from the internet. The database only accepts connections from the runtime within your local network. The runtime itself only makes outbound HTTPS connections to Atlan Cloud, which your network team can control through firewall rules.
See also
- Direct connectivity: How Atlan connects directly to data sources
- SDR connectivity: How Self-Deployed Runtime connects to data sources
- Set up Oracle: Configure user accounts and permissions
- What does Atlan crawl from Oracle?: Metadata extracted from Oracle